Fake Government Ransomware holds Android Devices Hostage: Learn How to Remove the Malware
6 min. read
Updated on
For those of you who don’t know, ransomware is a special class of Android malware which restricts access to the computer system and demands a ransom if you want the restriction to be removed.
In simple terms, ransomware is the ideal way to extort money from victims by holding their devices with personal data hostage.
We all know that Ransomware made its rounds on Windows, but it seems that it wants much more than that and now is targeting the Android operating system. A new piece of mobile malware claiming to be the government has made countless victims in the last few days, so that’s why we think that it is the ideal time to find out more about this fake government ransomware that holds Android smartphones and tablets hostage.
How is this Ransomware acting?
In case of being curios about the way that this new Android ransomware malware is acting, we can tell you that it requests full network access, as well as permission to run, to startup and even to prevent your Android handset from sleeping. This ransomware practically takes full control of the device, so that you won’t be able to use it properly anymore.
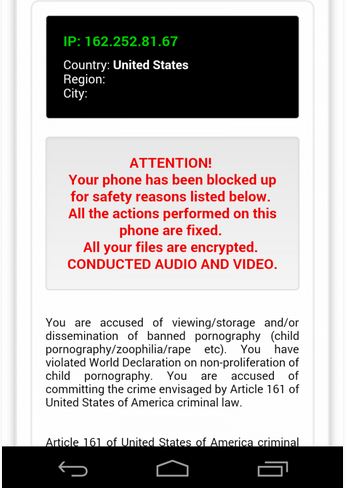
So, returning to the full network access that we have told you about, it seems that it allows the malicious app to communicate over the web and download the ransom message that will be shown on your captive device, as long as “you are accused of committing the crime envisaged by Article 161 of United States of America Criminal law”. Even more, the permission to run at startup and to prevent the handset from sleeping makes it impossible to escape the ransom message.
Now, seriously, do you think that FBI has nothing better to do than tracing you down and accusing you for storing copyrighted pornographic materials? But that’s the idea! In order to seem as serious as possible, the ransomware localizes fake government messages, depending on your GPS location, accusing you of viewing and downloading illegal porn content and demanding ransom.
Payment methods
The ransom that we are talking about is usually set at no more than $300 and as with any other regular ransomware, you’ll get detailed instructions on how to pay the ransom (which is called a “fine” in this case). We are referring to forms of payment such as MoneyPak as long as using SMS or any other phone-based payment is giving you a chance to follow the money trail and find the person behind this scam. But when it comes to prepaid electronic payment systems such as MoneyPak or vouchers that can be used to buy goods and other services online, they simply eliminate from the start any chance of doing that.
So, remember that ransomware doesn’t accept credit payments. Instead, it asks for payment in the form of vouchers or prepaid electronic systems, but don’t you think that if you pay the fine, you’ll get access to your Android files.
There have been reported numerous cases when the payment did not fixed the malware. In case of being in this situation, you are probably already feeling guilty about your activity and this is exactly what these people are relaying on. Many have fallen into this scam and more will come in case of not learning to be careful.
What should you do?
So, it really doesn’t matter what the on-screen message says; you do not pay the money under any circumstances! This is the wrong choice that might not even offer you a result! Don’t panic and for the moment try pressing the home button which will make the message disappear for a while. Anyway, it will pop up again, but at least you won’t have to stare at the same warning over and over again.
There are a few ransomware attacks cases that have been removed when the owners have simply rebooted their device. However, this might not work on your device as well. This ransomware is the most recent one, so we don’t have any removal tool to recommend you for the moment, but we’ll return with fresh details as soon as possible.
And if you cannot wait a few more days, just go with the Android device to the nearest service and see if there’s any chance to solve the ransomware problem.
What can you do to stay safe from this malware?
In the first place, you should know that ransomware is pushed automatically from fake porn sites visited by Android users via an .apk file that seems to be nothing more than an app. This malicious file that has the appearance of a harmless app ended up on tricking more and more people each day, so, in case of wondering what you should do in order to stay safe from this malware, our first advice is to abstain yourself from watching those porn videos.
Yes, the best thing you can do for yourself is to prevent ransomware from getting on your system by eliminating this risk, but don’t forget about the importance of being cautious when downloading apps from unofficial app markets as well. It is also recommended not to open any files that have been downloaded in your handset without any previous consent and don’t forget to use an antivirus for extra protection just in any case.
For example, all AVAST’s free and premium mobile security apps, avast! Mobile Security and avast! Mobile Premium choices are ideal when it comes to protecting you from anything containing any ransomware form. To be more precise, AVAST detects this ransomware under the name Android: Koler-A and immediately blocks its execution, so that your handset is completely safe. There are other antivirus options that you can choose from such as Norton Mobile Security (for Android smartphones and tablets, iPhone and iPad) or Symantec Mobile Security (which offers protection from mobile malware, privacy risks, greyware and other mobile threats), so the lack of choices is not an excuse that we can accept! They can defend against attacks that lead to ransomware and even detect and delete ransomware itself, so don’t hesitate to use this form of protection.
Ransomware has become far more common that we ever imagined and it shouldn’t be such a big surprise considering that there is no one to stop those people behind the idea to continue finding new victims.
We just hope that you are not one of them and remember to be cautious about everything that you are doing on your Android device!




User forum
0 messages