How to Solve Sensitive Data Exposure via WiFi Broadcasts in Android
A new vulnerability has been discovered in the Google Android operating system and it seems pretty capable to allow cyberattackers to covertly capture Wi-Fi broadcast data and track users. Researchers from Nightwatch Cybersecurity said in a security advisory that the bug, CVE-2018-9489, was discovered in the operating system’s communication management programming, so I bet that you are wondering if there is a way to solve this problem or not. It is something that you can do, but you might not like what you are about to read.
First of all, understand that system broadcasts by Android OS expose information about the user’s device to all applications running on the device. This normally includes the WiFi network name, BSSID, local IP addresses, the MAC address, as well as DNS server information. Even if some of this info is no longer available via APIs on Android 6 and higher versions, and extra permissions are normally required to access such data, by listening to these broadcasts, apps can capture the information, usually for legitimate purposes.
Therefore, attackers can geotrack users through the network name and BSSID by using database lookups, they may local Wi-Fi networks or use MAC addresses to track unique Android devices and not only. God knows how creative they might actually get!
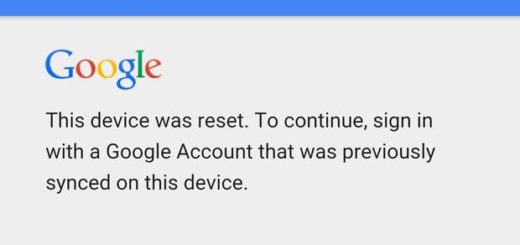
Even more, all versions of Android running on all devices affected including forks (such as Amazon’s FireOS for the Kindle), so what can you do about it? Well, there is one thing and one thing only when it comes to your power of solving this. It seems that Google Google is aware of the problem and solved these issues in Android P, so I can only encourage you to upgrade to Android 9.0 or later as soon as you can.
Despite of that, it does not plan to fix older versions. I told you that you might not like the sound of it, but at least you know now that Android P is not only a secret desire of your heart, but a necessity if the sensitive data exposure topic interests you.